While both are symmetric ciphers, stream ciphers are based on generating an infinite cryptograpic keystream, and using that to encrypt one bit or byte at a time (similar to the one-time pad), whereas block ciphers work on larger chunks of data (i.e. blocks) at a time, often combining blocks for additional . Other stream ciphers might vary the encryption of future parts of the message depending on previous parts. Some block cipher modes of operation actually create a synchronous stream cipher , like CTR and OFB mode. You should never reuse a key (and IV, if applicable) of a synchronous stream cipher.
Hash functions vs Stream Ciphers in terms of Speed Antwort 14. Diffusion in Stream Cipher Antwort 27.
Are Stream Ciphers Less Secure? Secure file transfer protocols like SFTP, FTPS, HTTPS, and WebDAVS encrypt data through symmetric key ciphers. These ciphers can be classified into two groups: stream ciphers and block ciphers. The basic difference lies in the logic used for the.
Advantages: Speed of transformation: algorithms are linear in time and constant in space. Low error propogation: an error in encrypting one symbol likely will not affect subsequent symbols. Disadvantages: Low difiusion: all information of a plaintext symbol is contained in a single ciphertext symbol.
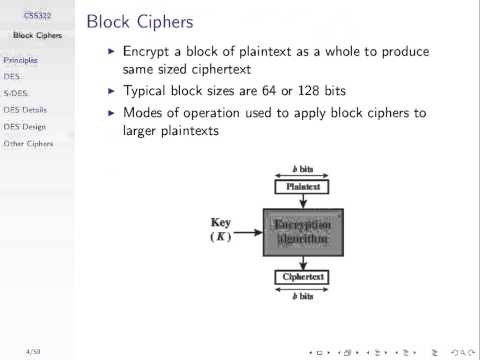
The major difference between a block cipher and a stream cipher is that the block cipher encrypts and decrypts a block . A cipher is a set of mathematical rules, or algorithm, used to convert readable text , or plaintext, into unreadable text, or ciphertext.
The principle difference between stream ciphers and block ciphers is that stream ciphers work on streams of text, one bit or one byte at a time, while block ciphers work on blocks . Idea of a block cipher : partition the text into relatively large (e.g. 1bits) blocks and encode each block separately. The encoding of each block generally depends on at most one of the previous blocks. Video created by University of Colorado System for the course Symmetric Cryptography. This module is about modern ciphers based on product ciphers.
Private-Key Encryption in Practice. We will then describe the. Katz Lindell, Chapter 5. FIPS publication describing DES (link on webpage). Lecture Notes 13: Private-Key Encryption in Practice.
In practice, people use direct constructions of candidate stream ciphers (PRGs with unbounded output length) and block ciphers . Eine Stromverschlüsselung, Stromchiffre oder Flusschiffre (englisch stream cipher ) ist ein kryptographischer Algorithmus zur symmetrischen Verschlüsselung, bei dem Zeichen des Klartextes mit den Zeichen eines Schlüsselstroms einzeln (XOR bei Bits) verknüpft werden. Der Schlüsselstrom ist normalerweise eine . The pseudorandom keystream is typically generated serially from a random seed value using digital shift registers. The seed value serves as the cryptographic key for decrypting the ciphertext stream.
Stream ciphers represent a different approach to symmetric encryption from block ciphers. In cryptography, a block cipher is a deterministic algorithm operating on fixed- length groups of bits, called a block, with an unvarying transformation that is specified by a symmetric key. Block ciphers operate on large .
Introduction: Symmetric-Key Crypto. A different “key” is generated . Some data transfer methods will encrypt data one byte at a time or in groups of larger data blocks. Groups of characters (in blocks).
Key is independent of plaintext and of ciphertext. Insertion, deletion can be detected. Synchronization required.